Concept
The problem most companies are still facing is that users need to be local administrators, typically to install software or to run legacy applications. To totally avoid this need, IT would have to script every piece of software any user may need - or alternatively, IT would have to manually install software for all users. Both are extremely time consuming and therefore the pragmatic solution is often to let users be local administrators and let User Account Control (UAC) handle it. Although UAC along with protective software does prevent most viruses, malware and ransomware being installed, attacks happen anyway. Here is why. What would your users do, if they see this?
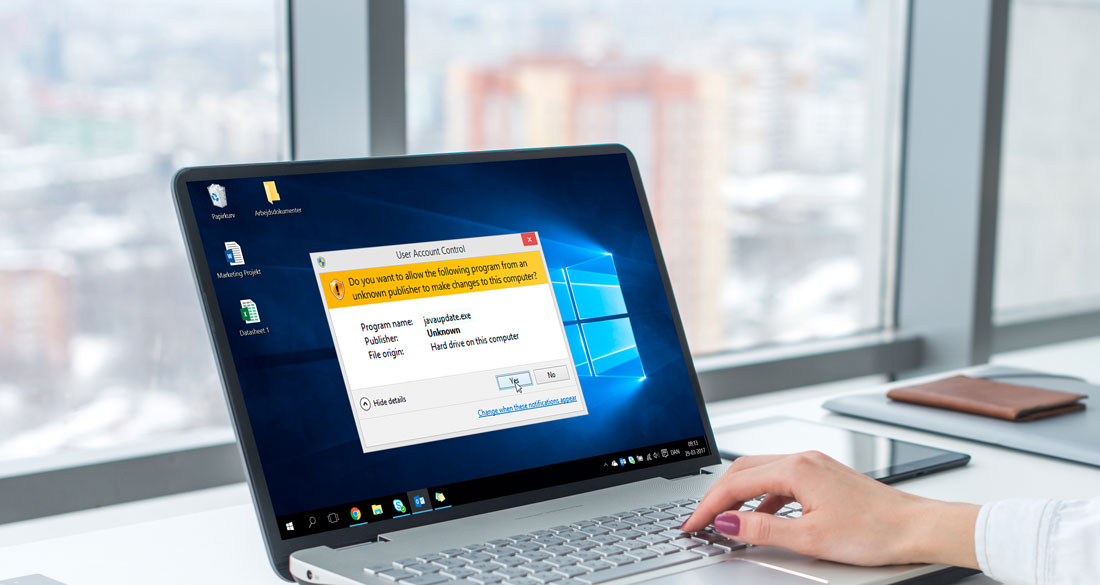
Java? Yes, I probably need that. All it takes is one user clicking "Yes". Think about that for a minute.
The user is not aware that there has to be a valid certificate from "Oracle America, Inc" for it to be the file they expected, nor can they be expected to know so. So the file on the image might very well be Russian ransomware. This is why you need Admin By Request (ABR). When you install ABR on clients, users are no longer local administrators by default, unless you give them a "time window". When users see the above, they would have to contact IT to get a time window to install first. If the user has a legitimate reason, you can approve the access. If the user says "We need to install AutoCAD for a new employee". All good, give them a time window. You still do not need to remote the user's computer to do the actual work and you can audit that the user actually did install only, what he or she said during the window.
Using Admin By Request: Requesting access
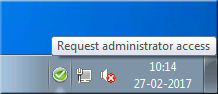
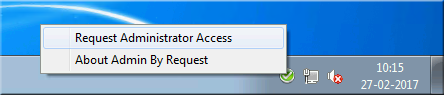
The user will see an icon in the system tray, which is green, when the user is not administrator. If the user needs to be administrator, the user would have to right-click and request permission
On this web site, you will see an inventory of your computers. You can click the "Live Demo" menu at the top to see, what it looks like. If a user has a legitimate need to be administrator, you locate the users' computer and click the "Admin Audit" tab, where you use the left-side window to approve one-time access:
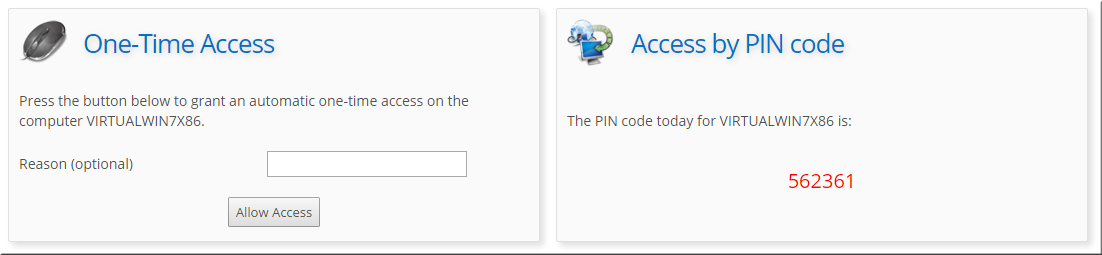
Once you have approved access, the user can request access one time before the end of the day. Under "My Account", you can configure how much time the user is administrator and you can also decide to auto-approve, in which case you will only audit. Once the user right-clicks and requests an administrator time window, the user will clearly see they are administrator and must be careful:
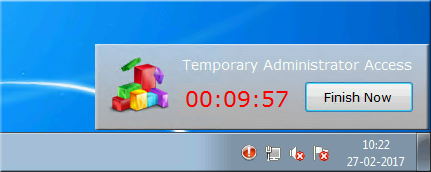
Once the user either stops the timer or the time runs out, the information will be uploaded to this website, so you can see when the window was started and stopped. You can also see which software was installed during the window. You can see a complete list of administrator usage on any given computer and you can also export the data to Excel, PDF file or a CSV file.
Legacy applications
Some legacy applications require local administrator rights, simply because they were written back in the day, when everything was open and using the same folder for application files and data was the norm. You can make a white-list of applications that will elevate automatically. Refer to the policies page for more information.
Offline Computers
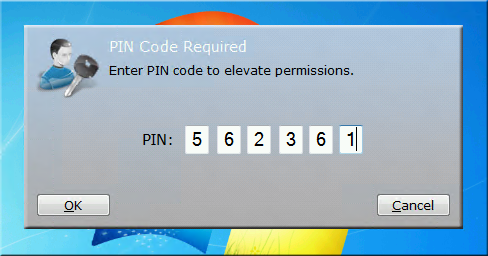
The user might need to be administrator offline (meaning without internet connection). In this case, the cloud server cannot be contacted and the user will be presented with a PIN code window instead. If you look at the screenshot further up, you can see that there is a PIN code on the right side. This is a PIN code that is unique for this computer on this day. Once the correct PIN code is entered, the window starts.
Questions?
If you are interested and would like to know more about Admin By Request functionality, book a free trial, or demo - please do get in touch and fill out the contact us form below - or initiate a live chat if available to get immediate answers!
test
<SmartDock> <RunScript>True</RunScript> <RunLogonScript>True</RunLogonScript> <RunAtStartup>False</RunAtStartup> <RunOnIPChange>True</RunOnIPChange> <RunOnIPLost>False</RunOnIPLost> <AutoRerun>True</AutoRerun> <IdleHours>24</IdleHours> <DailyRerun>False</DailyRerun> <DailyTime>00:00</DailyTime> <ExecDelayInSeconds>10</ExecDelayInSeconds> <LogEvents>False</LogEvents> <LogFile></LogFile> <StartupMessage>User logon</StartupMessage> <LogoffMessage>User logoff</LogoffMessage> <ReconnectMessage>User reconnected</ReconnectMessage> <DisconnectMessage>User disconnected</DisconnectMessage> </SmartDock>